BIOS and UEFI explained, all you need to know about
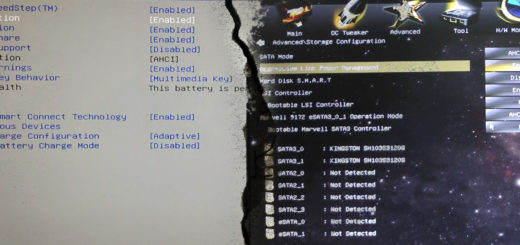
BIOS and UEFI are two of a kind, but completely different from each other. They serve one major purpose: booting the machine and they do it in different ways and with different options. Without them, all...














Recent Comments